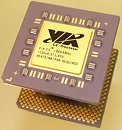
VIA C3 Processors Compromised by a Simple Shell Command
VIA processors probably make up an infinitesimal amount of the desktop PC market-share, and its makers market the chip only at pre-built machines such as digital-signage kiosks, information kiosks, ticket vending machines, ATMs, etc (which don't need a lot of processing power). At the Black Hat 2018 conference, security researcher Christopher Domas discovered that getting access to root privileges in Linux on a machine powered by VIA C3 "Nehemiah" processors is laughably easy. Just key in ".byte 0x0f, 0x3f" (without quotes) in any Linux CLI in user mode, and voila! You are now the root user.
Domas calls this his own iddqd (the cheat-code for "God Mode" in "Doom"). This backdoor, probably put in place by the processor's designers themselves, completely collapses the ring-based privilege system of the operating system, and elevates users and applications from the ring-2 (and above) userspace to ring 0 (root). It is an exploitation of a shadow-core, a hidden RISC processor within C7, which manages the startup, operation, and key storage of the x86 cores. Intel and AMD too have shadow-cores with similar functions.
Domas calls this his own iddqd (the cheat-code for "God Mode" in "Doom"). This backdoor, probably put in place by the processor's designers themselves, completely collapses the ring-based privilege system of the operating system, and elevates users and applications from the ring-2 (and above) userspace to ring 0 (root). It is an exploitation of a shadow-core, a hidden RISC processor within C7, which manages the startup, operation, and key storage of the x86 cores. Intel and AMD too have shadow-cores with similar functions.